A couple days ago I noticed a peculiar thing with my Vsun Android smartphone that’s running Android 6.0: on random occasions when I opened or while using Diode (an open source Reddit client app), the stock browser would pop up and open a webpage called Live Mobile Search (livemobilesearch.com).
The page is a search engine powered by Google however it’s has a Google Ad at the top of the page. While the search engine works, the ad refreshes upon typing and opens other search windows. This coupled with its automated launch quickly confirmed to me that this was likely an adware “virus”.
A cursory search online revealed that some android users were experiencing a similar issue with the adware. The earliest victim of this exact adware that I could find online was a StackExchnage question that dates back to 2017 though the adware seems to go as far back as 2012 going by this Android Central thread.
Nevertheless, the adware seems to have become more prevalent in the past few months if these Reddit threads are anything to go by. Personally, I noticed this around the 2nd week of March 2019.
Going by those other victims’ tales, the blame for the adware is likely an app that one may have installed recently. For some several Reddit victims, that app turned out to be the MegaN64 emulator.
For the rest however, the issue remains a big mystery since they claim they haven’t installed any new app recently. So what gives?
Preloaded Adware?
Well for me, this is hardly a new occurrence. This is the second time I’m noticing adware with this particular phone of mine.
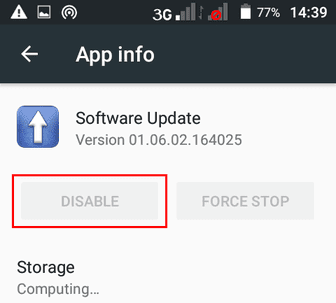
The first time was late last year when I noticed RevContent ads on my notification panel. After some of my investigations, it turned out that the Software Update app that came preinstalled on the phone was the one responsible for pushing the ads.
I couldn’t however uninstall that app since it was a System app and all my rooting attempts have failed thus far. The option to Disable was also unavailable for the app. Fortunately, clearing the data seemed to resolve the issue and I never encountered those ads again.
Three months later and a new adware has appeared. Coincidence? I don’t think so, though for a couple days there I was convinced it had to be a different app this time round.
It’s only after uninstalling a few recent apps with no success that I suspected the Software Update app was at it again. So I checked its app details and it turned it had accrued some new data this past few months without me noticing. Anyway, I cleared its app data and forced stop it.
I then went back and tried launching Diode and this time nothing happened. However, as I pointed out at the start of the article, the adware behaviour was random and consequently not all launches triggered it.
So I gave it a one-day grace period and kept launching Diode occasionally to see whether the ad would pop up. It never did until few days later.
How to Remove the livemobilesearch.com Adware
As you can tell clearing data and force stopping the app is a very temporary measure of dealing with this menace. This is because the app has a boot receiver which means it will launch every time you restart the device.
The only sure way of stopping the adware is either uninstalling or disabling the responsible app. But before you get there you need to establish which app is causing this.
Step 1: Find the App with Adware
If the adware started popping up only recently, first try uninstalling any apps you’ve installed of late. Do this one by one and try to trigger the adware after each uninstallation. This way you can establish the affected app and keep away from it in the future.
If you have no patience for this, just back up any data you need and do a factory reset.
On the other hand, if you haven’t installed any new app in the recent past, then it’s likely a system app is responsible. To trace the system app responsible, use the instructions provided in this answer.
You’ll need to enable USB Debugging in your phone and a PC to connect it to the Android Debug Bridge (ADB) so as to run the commands through Window’s command line.
Step 2: Remove the Affected System App
If you’ve root access, uninstall or freeze the affected System App. You can use an app like SD Maid or Titanium Backup to do that.
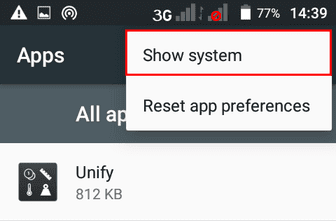
If you don’t have root access, try Disabling the app by going to go to the app’s details in Settings > Apps. Toggle the Show system option to view all the apps.
Chances are that you’ll find the app cannot be disabled. This was my situation as well.
Nevertheless, we may still be able to disable the app using ADB.
To do that:
1. First find out the package name of that system app. A quick easy way to do that is by using a System Info app like Elixir or use SD Maid by checking to the AppControl section.
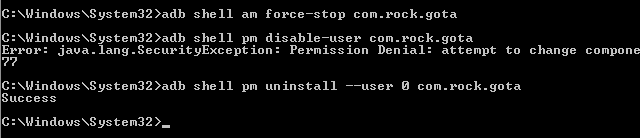
2. Now, with USB Debugging enabled, connect your phone to your PC send the following ADB command to the phone (replace com.rock.gota with your package name):
adb shell pm disable-user com.rock.gota
If it works, the command will reply Success.
In my case, it failed and returned the following error:
Error: java.lang.SecurityException: Permission Denial: attempt to change component state from pid=21031, uid=2000, package uid=10077
3. If you happen to get an error too, then the next thing we can try is to remove the app for the current primary user i.e. the app will be uninstalled for you, but will still be available for any other users you’ve created on that phone.
To do that, send the following command (replace com.rock.gota with your package name):
adb shell pm uninstall –user 0 com.rock.gota
Should it work, the command will reply Success. Hopefully it will as it was in my case.
4. Now just go back to your phone and in the app settings.
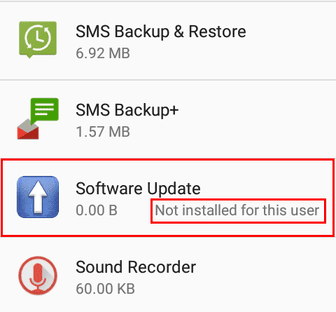
You should find either the app is disabled or is listed as not available for the current user as shown above.
Be Wary of Cheap Android Smartphones
As I concluded in my other article when I encountered the first adware, this issue is no doubt a deliberate scheme orchestrated by some unscrupulous manufacturers or vendors.
Their objective I take it is to create some kind of advertisement botnet (“adbotnet?”) which they can profit from long after selling their devices at very discounted prices. The obvious suspects here comprise mostly of smaller unknown brands of Chinese smartphones.
Unlike the great majority of small-time attackers that have to infect legitimate apps with their adware or software developers that resort to bundling their apps with the same, these manufacturers have a special advantage: preloading adware as a system app guarantees them security from detection and uninstallation.
This explains why the first victim I cited complained of the adware persisting even after doing a factory reset. Mind you, his device was a brand new smartphone (a Doogee Shoot 1). As it later turned out for several users with a similar device, the culprit was a system app called System Locker.
As such, be wary of cheap android brands that you don’t trust. That’s the only real long term solution to all this. Couple this measure with downloading apps only from Google Play Store or other reputable app stores like F-droid.
Side note: (since I’ve noticed people have the habit of carrying the Window’s ecosystem mentality to Android) don’t rely on installing Android anti-viruses as they won’t do much for this types of malware and the same goes for the myriad of “cleaners” out there that don’t do much other than display ads. As one would say, the best antivirus is you the user.